Why manufacturers must prioritize network security

TL;DR:
- Manufacturing is increasingly targeted by cybercriminals exploiting outdated OT systems and interconnected networks.
- Regulatory requirements in Singapore and ASEAN now mandate cybersecurity measures, risk assessments, and threat sharing.
- Proactive security investments, including network segmentation, continuous monitoring, and incident planning, are critical for resilience.
Manufacturing has always been a high-stakes environment, but the threat landscape has shifted dramatically. Ransomware attacks cost Norsk Hydro $71 million and shut down production for weeks, while Bridgestone faced plant shutdowns across multiple continents with losses estimated between $100 million and $150 million. These are not edge cases. For manufacturing executives and IT leaders across Singapore and ASEAN, the question is no longer whether your operations will be targeted, but whether your network is prepared to absorb the hit. This article gives you the evidence, regional context, and practical steps you need to act now.
Table of Contents
- The evolving cybersecurity risk for manufacturers
- Regulatory landscape: Singapore and ASEAN in focus
- The business and operational impacts of poor network security
- Strengthening defenses: Key strategies for manufacturers
- Why manufacturers can’t afford to take a passive approach
- How AGR Networks empowers secure manufacturing growth
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cyber risks are business risks | Manufacturers face costly, business-halting attacks that require immediate management attention. |
| Compliance is getting tougher | New regional regulations like the OT Masterplan 2024 demand advanced cybersecurity for manufacturers. |
| Invest in OT skills | Workforce capabilities and strategic partnerships are key to building resilient network security. |
| Act before it’s too late | Proactive investments are more effective and affordable than responding after a breach. |
The evolving cybersecurity risk for manufacturers
Manufacturing has quietly become one of the most targeted sectors for cybercriminals globally. The reasons are not hard to understand. Factories run on operational technology (OT), which refers to the hardware and software that monitors and controls physical equipment, processes, and infrastructure. Historically, OT systems ran in isolation. Today, they are connected to corporate IT networks, cloud platforms, and supplier systems. That connectivity creates enormous efficiency gains, and an equally enormous attack surface.
Attackers have taken notice. Ransomware groups specifically target manufacturers because the cost of downtime is immediate and severe. A factory floor that goes dark for 24 hours does not just lose revenue. It disrupts supply chains, breaks contractual commitments, and can damage equipment that depends on continuous operation. Threat actors exploit this urgency to demand larger ransoms, knowing that a manufacturer’s fastest path to recovery is often payment.
The Norsk Hydro attack is a defining case study. The Norwegian aluminum giant was hit by the LockerGoga ransomware in 2019, forcing it to switch many operations to manual processes. The financial damage reached $71 million. Bridgestone’s 2022 incident forced plant shutdowns across North America, Latin America, and other regions, with estimated losses of $100 million to $150 million. Both attacks exploited weaknesses that are common in manufacturing environments: outdated systems, insufficient network segmentation, and slow detection times.
The key vulnerabilities that make manufacturers attractive targets include:
- Legacy OT systems that were never designed with cybersecurity in mind and cannot easily be patched or updated
- Flat network architectures where a single compromised endpoint can reach critical production systems
- Third-party vendor access that introduces risk through supplier portals, remote maintenance tools, and shared credentials
- Limited visibility into OT traffic, making it difficult to detect unusual behavior before damage is done
- Workforce gaps where staff are trained for production efficiency but not for cyber threat recognition
“The integration of IT and OT is not a future trend. It is the current reality, and most manufacturers in ASEAN are still securing these environments with tools and practices designed for a different era.”
For Singapore and ASEAN manufacturers specifically, the risk is compounded by the region’s role as a global supply chain hub. A breach at a single facility in Johor, Batam, or the Jurong Island industrial zone can have cascading effects across multiple countries and industries. If you want to understand how to build a ransomware response playbook before an incident occurs, that preparation starts with understanding exactly how exposed your current network is.
Regulatory landscape: Singapore and ASEAN in focus
Cybersecurity regulations for manufacturers in Singapore and ASEAN are tightening, and the pace of change is accelerating. Regulators are no longer treating cybersecurity as a voluntary best practice. It is becoming a legal and operational requirement with real consequences for non-compliance.
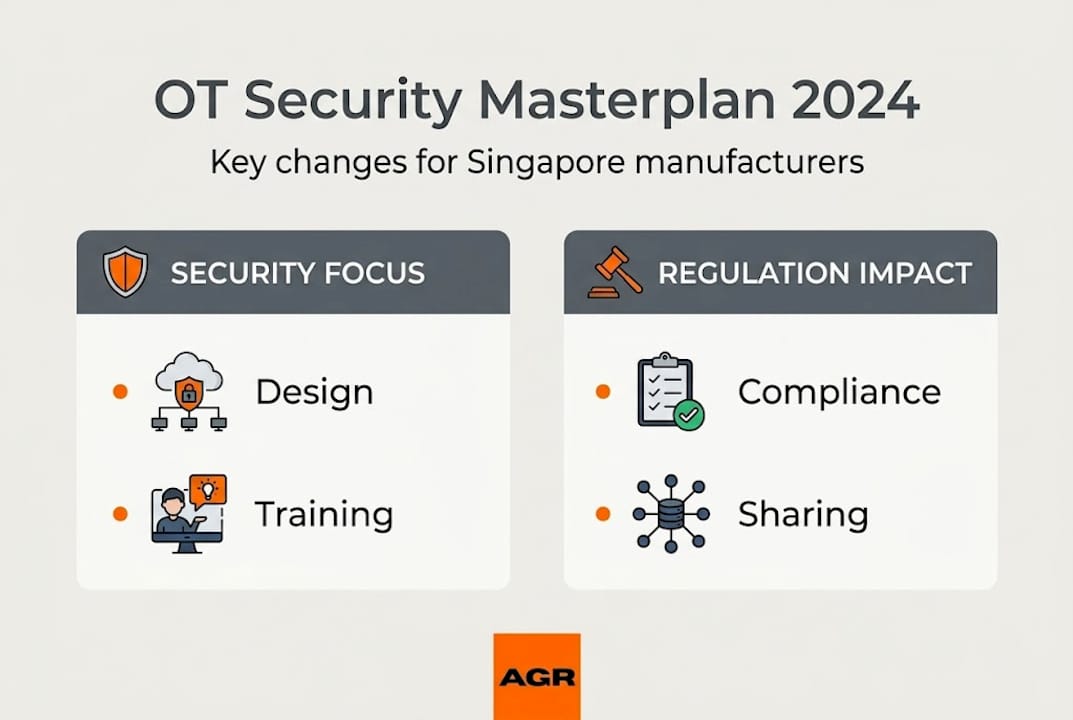
Singapore’s Cyber Security Agency (CSA) released the OT Cybersecurity Masterplan 2024, which sets a clear direction for industrial operators. The Masterplan promotes security-by-design principles, meaning cybersecurity must be built into systems from the ground up rather than bolted on afterward. It also emphasizes talent pipeline development through the OT Cybersecurity Competency Framework (OTCCF) and the establishment of OT-ISAC, a threat intelligence sharing platform for industrial operators. The ASEAN OT cybersecurity market is projected to grow at a 16.95% compound annual growth rate, reaching $14.1 billion by 2031.
Here is a quick comparison of key regulatory requirements affecting manufacturers in the region:
| Regulation / Framework | Scope | Key Requirement | Impact on Manufacturers |
|---|---|---|---|
| OT Masterplan 2024 | Singapore industrial operators | Security-by-design, OT-ISAC participation | Mandatory risk assessments and reporting |
| Critical Information Infrastructure (CII) Act | 11 critical sectors including manufacturing | Regular audits, incident reporting | Fines and operational restrictions for breaches |
| PDPA (Singapore) | All organizations handling personal data | Data protection policies and breach notification | Applies to HR, customer, and supplier data |
| ASEAN Cybersecurity Cooperation Strategy | Regional | Cross-border threat sharing | Influences national policy in member states |
The consequences of falling behind on compliance are significant. Manufacturers classified as Critical Information Infrastructure (CII) operators face mandatory audits, incident reporting obligations, and potential fines or operational restrictions for non-compliance. Even companies that do not fall under CII classification are subject to the Personal Data Protection Act (PDPA), which governs how employee, customer, and supplier data is handled. You can review PDPA and IT compliance requirements to understand where your data management practices stand today.
For manufacturers in financial services adjacent supply chains, the MAS TRM guidelines also carry indirect relevance, particularly when your operations touch payment systems or financial data flows.
The compliance burden is real. But there is an upside. Manufacturers that invest early in meeting these requirements build a security posture that becomes a competitive advantage. Customers, particularly large multinationals and government-linked entities, increasingly require suppliers to demonstrate cybersecurity certifications and audit readiness. Early movers gain access to contracts that laggards cannot qualify for.
Pro Tip: Start your compliance journey by mapping all OT assets and their connections to IT systems. This single exercise often reveals gaps that no regulation required you to find, but that attackers would have exploited within months.
The business and operational impacts of poor network security
The financial cost of a cyberattack is just the beginning. The full business impact of poor network security spreads across operations, customer relationships, and long-term reputation in ways that are difficult to quantify but impossible to ignore.
Consider the two most instructive cases from recent years. The Norsk Hydro incident forced the company to revert to manual operations across multiple plants. Aluminum production, a continuous process that cannot simply pause and restart, was severely disrupted. Recovery took weeks. The $71 million cost covered IT restoration, lost productivity, and reputational management. Bridgestone’s attack followed a similar pattern, with plants across two continents going offline simultaneously, disrupting tire supply to automotive manufacturers who depend on just-in-time delivery.

Here is how short-term and long-term impacts compare for manufacturers:
| Impact Type | Short-term (0 to 30 days) | Long-term (30 days to 2 years) |
|---|---|---|
| Financial | Ransom payments, emergency IT costs | Insurance premium increases, lost contracts |
| Operational | Production halts, manual workarounds | Process redesign, system replacement |
| Reputational | Customer and media scrutiny | Supplier disqualification, brand erosion |
| Regulatory | Incident notification obligations | Audits, fines, increased oversight |
| Human | Staff overtime, stress, key person risk | Talent attrition, recruitment difficulty |
The cascading effects on supply chains deserve particular attention. Modern manufacturing supply chains are tightly coupled. When one node fails, the disruption travels upstream and downstream within hours. A Singapore-based component manufacturer that goes offline for 72 hours can halt assembly lines in Thailand, Malaysia, and Vietnam. Automotive, electronics, and pharmaceutical manufacturers are especially exposed because their production tolerances for delay are extremely low.
Vendor and supplier risk adds another layer. Many breaches do not start inside the target organization. They enter through a third-party vendor with legitimate access to the network. A supplier’s compromised credentials become your problem the moment they connect to your systems.
The numbered steps below show how a typical breach escalates in a manufacturing environment:
- An attacker gains access through a phishing email sent to a maintenance contractor
- Credentials are used to access a remote maintenance portal connected to the OT network
- Ransomware is deployed across both IT and OT systems simultaneously
- Production halts as PLC (programmable logic controller) commands are disrupted
- The company faces a choice between paying the ransom or rebuilding systems from backup
“The most expensive moment in cybersecurity is always the one after an attack. Every dollar spent on prevention returns multiples in avoided recovery costs.”
Staying current on known vulnerabilities is part of the defense. Reviewing resources like the Fortinet vulnerability advisory gives your team specific, actionable intelligence on threats targeting the firewall and network equipment you may already have deployed. Understanding the full scope of manufacturing IT solutions available to you is the first step toward closing these gaps systematically.
Strengthening defenses: Key strategies for manufacturers
Knowing the risk is not enough. You need a clear, prioritized action plan that fits the realities of a manufacturing environment: legacy systems, 24/7 operations, limited downtime windows, and a workforce primarily trained for production rather than security.
The most effective strategies combine technology, process, and people. Here is where to focus:
- Network segmentation: Separate your OT network from your corporate IT network using firewalls and demilitarized zones (DMZs). This limits the blast radius if either side is compromised. A flat network is an attacker’s best friend.
- Continuous monitoring: Deploy OT-aware monitoring tools that can detect anomalies in industrial protocols like Modbus, DNP3, and PROFINET. Standard IT monitoring tools often miss OT-specific threats entirely.
- Incident response planning: Develop and test a manufacturing-specific incident response plan that cover