Step-by-step network management for IT leaders in Singapore

TL;DR:
- FCAPS provides a structured, repeatable framework for managing complex enterprise networks.
- Consistent application of FCAPS improves network reliability, compliance, and incident resolution.
- Treating FCAPS as a daily operational discipline enhances overall network performance and security.
Managing a complex enterprise network across multiple sites, user groups, and compliance requirements is genuinely difficult. Even experienced IT leaders can find themselves reacting to incidents rather than running a structured operation. The FCAPS model, which organizes network management into Fault, Configuration, Accounting, Performance, and Security, gives you a clear, repeatable framework to work from. This guide walks you through each step with practical actions, tools, and decision points built for Singapore and ASEAN enterprise environments.
Table of Contents
- Understanding the FCAPS framework in network management
- Step 1: Fault management – identifying and resolving issues
- Step 2: Configuration management – standardizing and monitoring your network
- Step 3: Performance and security management – optimizing and protecting your network
- What most Singaporean CIOs miss: the power of FCAPS as a daily workflow
- Transform your network management with enterprise solutions from AGR Networks
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| FCAPS simplifies complexity | Using FCAPS helps IT leaders break network management into clear, actionable steps. |
| Diagnose faults efficiently | Packet capture and structured troubleshooting accelerate issue resolution and minimize downtime. |
| Standardize configurations | Consistent configuration management reduces risks and supports compliance in enterprise networks. |
| Monitor performance and security | Regular monitoring and security checks safeguard network reliability and protect data. |
| Leverage expert solutions | Expert-managed IT services can extend these step-by-step strategies and boost operational effectiveness. |
Understanding the FCAPS framework in network management
Before you can manage a network well, you need a consistent way to think about it. Ad hoc troubleshooting works occasionally, but it creates blind spots and inconsistent outcomes across teams. The FCAPS ISO model defines five functional areas of network management and is recognized as an industry standard developed under the OSI-ISO framework.
The five areas are:
- Fault management: Detecting, diagnosing, and resolving network failures
- Configuration management: Standardizing, tracking, and controlling device settings
- Accounting management: Monitoring resource usage and allocating costs or capacity
- Performance management: Measuring throughput, latency, and availability against baselines
- Security management: Enforcing access policies, auditing threats, and maintaining compliance
Each area is distinct, but they work together. A configuration error can trigger a fault. A security incident can degrade performance. Treating these areas as isolated tasks is where most IT teams run into trouble.
Why FCAPS matters for Singapore enterprises
Singapore’s enterprise IT environment is demanding. You are managing regulatory obligations under PDPA, MAS TRM guidelines, and sector-specific frameworks, while also supporting hybrid workforces and multi-site operations across the region. A structured model like FCAPS gives your team shared language, clear ownership, and a process to follow when things go wrong.
| FCAPS area | Primary goal | Common tool category |
|---|---|---|
| Fault | Detect and resolve failures | SNMP monitors, alerting platforms |
| Configuration | Standardize and track changes | CMDB, config backup tools |
| Accounting | Track usage and allocate resources | NetFlow analyzers, billing tools |
| Performance | Measure and optimize network health | APM, bandwidth monitoring |
| Security | Enforce policies and detect threats | SIEM, firewalls, access control |
Organizations that apply FCAPS consistently report faster mean time to resolution, fewer change-related outages, and stronger audit readiness. If you are building or scaling your IT infrastructure solutions, FCAPS gives you the operational backbone to do it reliably.
Step 1: Fault management – identifying and resolving issues
Fault management is where most IT teams spend the most unplanned time. Without a structured approach, you end up chasing symptoms rather than causes. Fault management follows a defined sequence: direction, diagnosis, correlation, restoration, and resolution. Each step has a specific purpose.
The five-step fault management process:
- Direction: Identify which part of the network is affected. Use topology maps and SNMP alerts to narrow the scope quickly. Avoid jumping to conclusions based on user reports alone.
- Diagnosis: Isolate the specific device, link, or service causing the issue. Check logs, interface error counters, and event timestamps.
- Correlation: Determine whether multiple alerts are symptoms of a single root cause. A router failure can generate dozens of downstream alerts that appear unrelated.
- Restoration: Restore service as quickly as possible, even if the root cause is not yet fully identified. This may mean failing over to a backup link or rerouting traffic.
- Resolution: Fix the actual root cause, document the incident, and update your runbooks.
Handling intermittent failures
Intermittent failures are the hardest category to manage. They appear and disappear before you can capture enough data. Packet capture near the ambiguity point is often decisive for root-cause isolation and is associated with faster detection outcomes in complex environments.
Place a capture tool at the boundary between where the failure is observed and where the network appears healthy. Look for retransmissions, out-of-order packets, and TCP window size changes. These patterns often reveal physical layer issues, misconfigured QoS policies, or upstream provider problems that standard monitoring misses.
Pro Tip: Set up continuous packet capture on critical segments with rolling buffers. When an intermittent fault occurs, you already have the data. You do not need to wait for it to happen again.
| Fault type | Detection method | Recommended action |
|---|---|---|
| Link flapping | Interface error counters | Check physical cabling, SFP modules |
| Intermittent drops | Packet capture, flow analysis | Analyze retransmits, check QoS |
| Device unreachable | ICMP/SNMP polling | Verify power, check routing table |
| Partial outage | Correlation across alerts | Trace to upstream device or ISP |
For enterprises running managed IT services, having a 24/7 NOC that follows this exact sequence means faults are handled consistently, even outside business hours.
Step 2: Configuration management – standardizing and monitoring your network
After you have a solid fault management process, configuration management is what prevents many faults from occurring in the first place. Most network outages trace back to a configuration change, whether it was planned, undocumented, or made under pressure during an incident.

Configuration management has three core objectives: standardize device settings, track every change, and ensure you can restore a known-good state quickly.
Key practices for enterprise configuration management:
- Establish a configuration baseline for every device type. Document the approved settings for your switches, routers, firewalls, and wireless controllers. Any deviation from baseline is a change that needs to be reviewed.
- Implement a formal change control process. Every change should have a ticket, an approval, a rollback plan, and a post-change verification step. This applies to minor changes too.
- Automate configuration backups. Schedule daily or weekly backups of device configurations to a version-controlled repository. If a device fails or is misconfigured, restoration takes minutes rather than hours.
- Use a CMDB (Configuration Management Database) to maintain an accurate inventory of all network assets, their settings, and their relationships to other systems.
“Configuration drift is one of the most common causes of hard-to-diagnose network issues. When a device’s running configuration no longer matches its intended baseline, you are troubleshooting a problem that should not exist.”
Compliance and regulatory alignment
In Singapore, configuration management directly supports regulatory compliance. MAS TRM guidelines require financial institutions to maintain accurate records of IT assets and configurations. PDPA obligations extend to network-level controls that protect personal data in transit. Your configuration management process is not just an operational tool; it is an audit artifact.
When evaluating firewall platforms for your enterprise, a structured firewall comparison helps you align device capabilities with your compliance and performance requirements from the start.
Pro Tip: Review your IT readiness checklist before any major network change. It surfaces gaps in documentation and process that become critical during audits or incidents.
For hospitality and mixed-use environments, configuration management gets more complex when you are integrating property management systems with network infrastructure. Hotel PMS network integration is a good example of where configuration standards must account for third-party systems and guest-facing services simultaneously.
If you are evaluating managed service contracts, the configuration management scope is one of the most important areas to clarify. Review the key questions for managed IT contracts to ensure your provider maintains your configuration standards consistently.
Step 3: Performance and security management – optimizing and protecting your network
Once your network configuration is standardized, focus shifts to keeping your network fast, reliable, and secure. Performance management and security management are the two areas that most directly affect your users and your risk profile.
Performance management: baselines, monitoring, and anomaly detection
Performance management starts with measurement. You cannot optimize what you have not measured, and you cannot detect anomalies without a baseline to compare against.
Start by establishing baselines for the following metrics across all critical segments:
- Latency: Round-trip time between key endpoints, particularly for voice and video traffic
- Throughput: Actual bandwidth utilization versus available capacity on each link
- Packet loss: Even 0.5% packet loss can significantly degrade VoIP and real-time application quality
- Availability: Uptime percentage per device and per link, tracked over rolling 30-day periods
- Error rates: Interface error counters, CRC errors, and input/output drops
Once baselines are established, configure threshold-based alerts. When a metric deviates significantly from its baseline, your team is notified before users start calling. This shifts your operation from reactive to proactive.
The FCAPS performance layer also includes capacity planning. Review your baseline trends quarterly. If a link is consistently running above 70% utilization, plan an upgrade before it becomes a bottleneck. This is especially relevant for ASEAN enterprises with growing branch office footprints and increasing cloud traffic volumes.
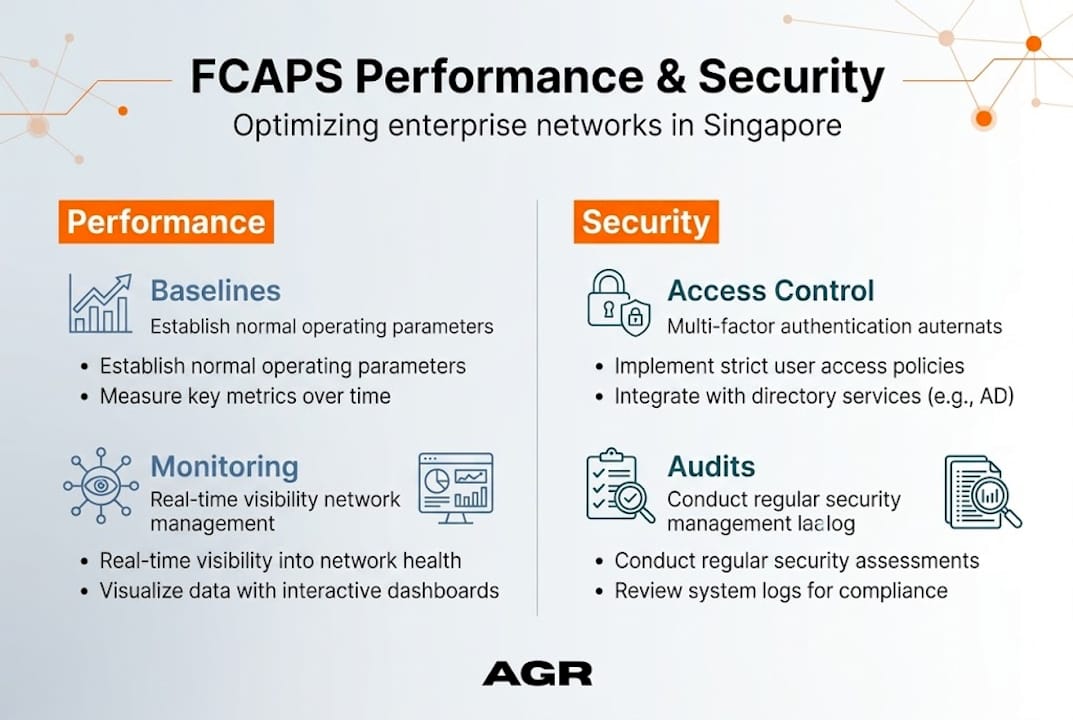
Security management: access control, policy enforcement, and audits
Security management within FCAPS is not a replacement for a full cybersecurity program. It is the network-level layer that enforces your security policies and provides visibility into threats.
Core security management practices include:
- Network segmentation: Use VLANs and firewall zones to separate user groups, servers, IoT devices, and guest traffic. Flat networks amplify the impact of any breach.
- Access control policies: Implement role-based access to network management interfaces. No engineer should have unrestricted access to all devices without an audit trail.
- Regular securit